How often do you think about the Roman Empire? And what about data security? If you have answered ‘never’ twice, I’ve got some news for you: you are not a man, not yet a developer. However, Retool Devs can sleep tight every night, because the Retool Team understands how important it is to keep your info safe. And that should be a top priority for you too, if you're building custom apps.
In this article, we will concentrate on how to manage user permissions in Retool and how to craft a user experience personally, even on Free or Team pricing plans.
How does Retool handle user permissions and access levels?
Retool has a built-in user management system available on their Business and Enterprise plans. This system lets you control exactly who can peek at and tinker with your apps, resources, and workflows. Here are two major concepts: groups and levels. Let’s start with groups.
Try to imagine a project where only specific team members can see documents. Permission groups in Retool work similarly. You create groups for users with similar roles (something like "Marketing Team" or "General Cleaning Division"). Then, you assign permission levels to those groups. These levels determine what each group member can do with your precious data.
Okay, we’ve met the word ‘levels’. Retool has three access levels: Use, Edit, and Own. Use is the basic level for your end-users. Accounts with this level can view and interact with the assigned app, resource, or workflow, but they can't make any changes. Think of it as read-only access.
Edit: This level unlocks some modification capabilities. You can still view and use apps and resources, but now you can also modify them. This access level is an ideal option for those who are more tech-aware and can make some adjustments by themselves.

Okay, but what to do if this granularity isn’t enough for your project? Or isn’t available, as long you are using the Free or Team plan? Let’s manage it by ourselves.
Developing an Access Control List
We should start from the designing permissions to achieve the desired granularity level. Try to study your current business flows to understand how many different operations your team members have and describe them. Just to note: better avoid overlapping permissions. For example, it’s okay to have ‘Can Make Coffee’ and ‘Can Make Tea’ permissions, but not okay to have something like ‘Can Make Coffee’ and ‘Can Make Coffee and Tea’.
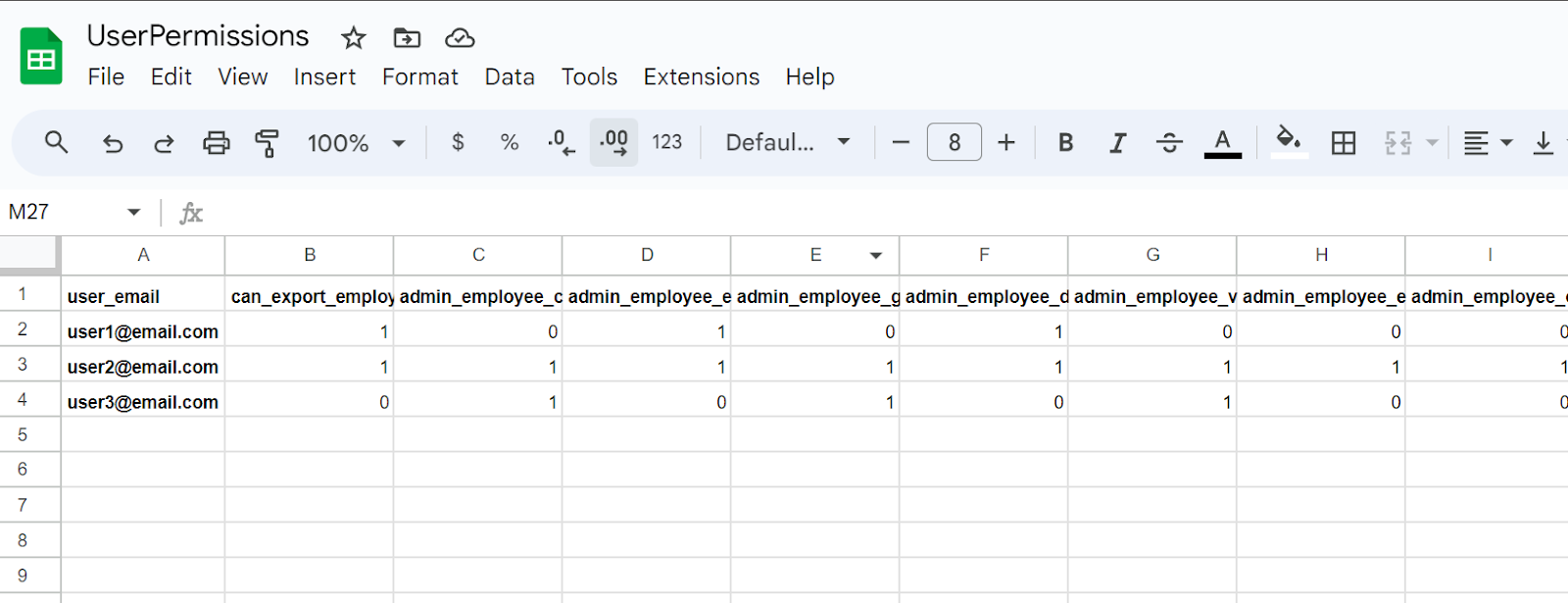
A free-to-use and convenient way to manage permissions might be a Google Sheet. Just organize your permissions as column headers, while in row titles put user emails. On the intersection of these two, you can put, to say, 0, if the permission is not granted to a user, and 1, if it is. Remember, it’s just an example. If you are already using an advanced ACL system, you can still benefit from these ideas.
Now we are ready to proceed with applications.
Securing UI: How to disable buttons and other controls based on permissions
As long as we use a Google Sheet Document in this article, we are limited in our ability to filter data on the application side. Each user will store on their device a full configuration of all the users. This is not safe, is it?
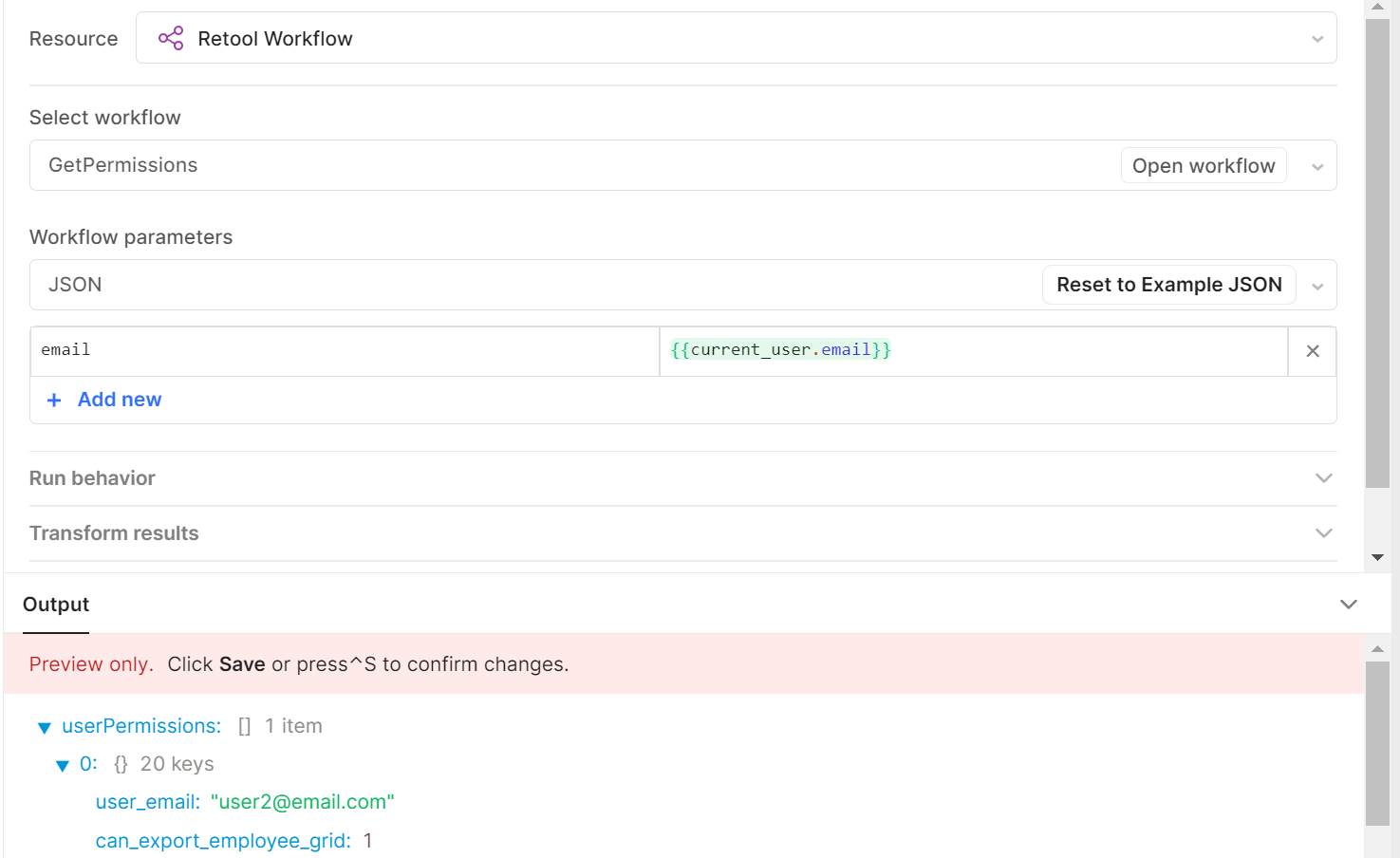
To avoid this issue, let’s create a workflow. I’ve named it ‘GetPermissions’. It takes the user's email as input and returns only permissions that correspond to the active user.

Now it’s time to create a corresponding call of the workflow inside of the app. As an input, we will provide the reference to {{current_user.email}}. This query will return a set of permissions assigned to the user, or nothing if the user doesn’t exist.
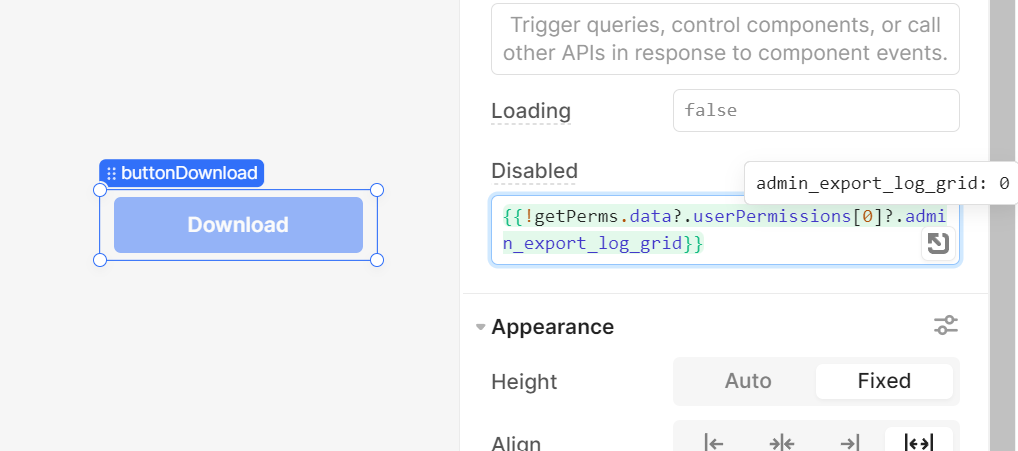
What is left? Now we have to go to the UI components level: we can either hide or disable them based on permissions. What option is better depends on your project. Just go to the Inspector and refer to the permission you are going to check. Don’t forget to use ?. – the optional chaining operator. This will allow you to handle situations when a given permission doesn’t exist at all. Not using the optional chaining operator, in case of absence of property, Retool will fail to evaluate the expression – and will replace it with false. That’s not what we need!
Now we are good to go to the queries. Believe it or not, it’s even more interesting!
Securing SQL queries with custom user permissions
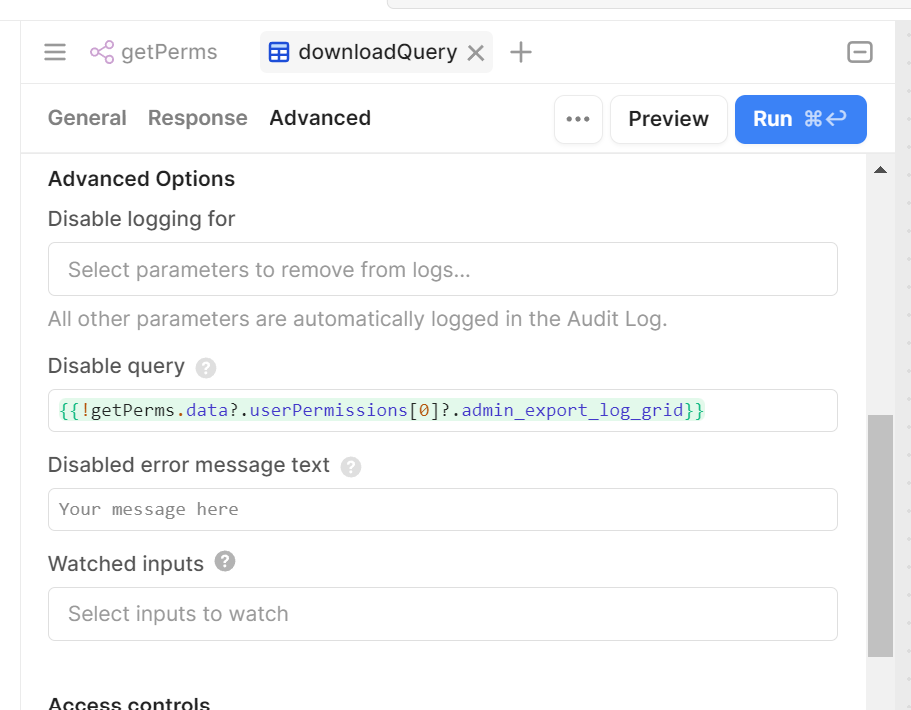
Okay, first of all, you can use the same approach as we have just demonstrated for UI components. To do so, just open the Advanced tab of the query editor and scroll down to the ‘Disable Query’ setting. Here you can put an expression that also should be correctly calculated either to false or true. In our example, the user doesn’t have the right to run this query, that’s why it won’t be run, even if the user ‘hacks’ your application and re-enables the ‘Download’ button back. Don’t forget the put the ‘?’ before the ‘.’ to correctly handle a case of absent permissions.
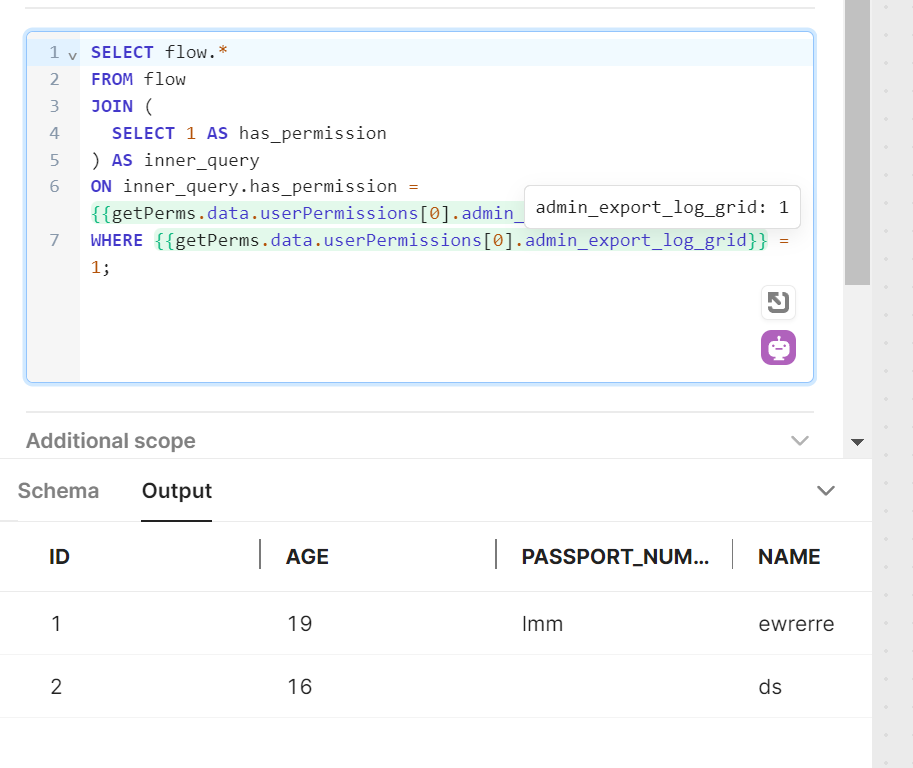
Is this enough? Yes, in most cases. But what if a user spoofs the data on his or her side, and re-enables back both the button and the query? Let’s add one more check. Now we will inject a permission check directly into the SQL query.
To do so, we should refer to permission in a WHERE clause to return rows only if the permission exists and equals 1. Nothing tricky, but to avoid problems with prepared statements enabled, we should wrap this check into a JOIN statement or a subquery. And remember: here’s the place we use the regular chaining operator ‘.’

Looks like we are all good! Just imagine: we have just implemented a simple access control system that works on no-paid tools. By the way, this approach is a simple fork of the solution that we have covered in the previous article. The only huge difference is that we use embedding user permissions inside the current_user object – but all other steps remain the same. Good luck!
---
Dmitry is the Head of Low-Code Department at Akveo. With a rich background in media and marketing, Dmitry brings an extraordinary look at the world of IT technologies. He is deeply passionate about finding the most effective and elegant solutions to complex client problems. In our blog articles, Dmitry will share his expertise in Retool and other low-code platforms to offer you valuable insights on Retool to enhance business process efficiency.
Streamlining Gifting Marketplace Operations with Retool
Afloat, a gifting marketplace, needed custom dashboards to streamline order management, delivery tracking, and reporting while integrating with Shopify and external APIs.
The solution:
We built two Retool-based dashboards:
- A Retail Partner Dashboard embedded into Shopify for managing orders and store performance.
- An Admin Dashboard for handling deliveries and partner data.
Both dashboards included real-time integration with Afloat's Backend and APIs for accurate, up-to-date data and scalability.
The result: enhanced efficiency, error-free real-time data, and scalable dashboards for high-order volumes.
Billing Automation for a SaaS Company with Low-Code
Our client needed a robust billing solution to manage hierarchical licenses, ensure compliance, and automate invoicing for streamlined operations.
The solution:
We developed a Retool-based application that supports multi-tiered licenses, automates invoicing workflows, and integrates seamlessly with CRM and accounting platforms to enhance financial data management.
The result:
- Achieved 100% adherence to licensing agreements, mitigating penalties.
- Automated invoicing and workflows reduced manual effort significantly.
- Dashboards and reports improved decision-making and operational visibility.
Retool Dashboards with HubSpot Integration
Our client needed a centralized tool to aggregate account and contact activity, improving visibility and decision-making for the sales team.
The solution
We built a Retool application integrated with HubSpot, QuickMail, and Clay.com. The app features dashboards for sorting, filtering, and detailed views of companies, contacts, and deals, along with real-time notifications and bidirectional data syncing.
The result
- MVP in 50 hours: Delivered a functional application in just 50 hours.
- Smarter decisions: Enabled data-driven insights for strategic planning.
- Streamlined operations: Reduced manual tasks with automation and real-time updates.
Lead Generation Tool to Reduce Manual Work
Our client, Afore Capital, a venture capital firm focused on pre-seed investments, aimed to automate their lead generation processes but struggled with existing out-of-the-box solutions. To tackle this challenge, they sought assistance from our team of Akveo Retool experts.
The scope of work
The client needed a tailored solution to log and track inbound deals effectively. They required an application that could facilitate the addition, viewing, and editing of company and founder information, ensuring data integrity and preventing duplicates. Additionally, Afore Capital aimed to integrate external tools like PhantomBuster and LinkedIn to streamline data collection.
The result
By developing a custom Retool application, we streamlined the lead generation process, significantly reducing manual data entry. The application enabled employees to manage inbound deals efficiently while automated workflows for email parsing, notifications, and dynamic reporting enhanced operational efficiency. This allowed Afore Capital's team to focus more on building relationships with potential founders rather than on administrative tasks.
Retool CMS Application for EdTech Startup
Our client, CutTime, a leading fine arts education management platform, needed a scalable CMS application to improve vendor product management and user experience.
The scope of work
We developed a Retool application that allows vendors to easily upload and manage product listings, handle inventory, and set shipping options. The challenge was to integrate the app with the client’s system, enabling smooth authentication and product management for program directors.
The result
Our solution streamlined product management, reducing manual work for vendors, and significantly improving operational efficiency.
Building Reconciliation Tool for e-commerce company
Our client was in need of streamlining and simplifying its monthly accounting reconciliation process – preferably automatically. But with a lack of time and low budget for a custom build, development of a comprehensive software wasn’t in the picture. After going through the case and customer’s needs, we decided to implement Retool. And that was the right choice.
The scope of work
Our team developed a custom reconciliation tool designed specifically for the needs of high-volume transaction environments. It automated the processes and provided a comprehensive dashboard for monitoring discrepancies and anomalies in real-time.
The implementation of Retool significantly reduced manual effort, as well as fostered a more efficient and time-saving reconciliation process.
Creating Retool Mobile App for a Wine Seller
A leading spirits and wine seller in Europe required the development of an internal mobile app for private client managers and administrators. The project was supposed to be done in 1,5 months. Considering urgency and the scope of work, our developers decided to use Retool for swift and effective development.
The scope of work
Our developers built a mobile application tailored to the needs of the company's sales force: with a comprehensive overview of client interactions, facilitated order processing, and enabled access to sales history and performance metrics. It was user-friendly, with real-time updates, seamlessly integrated with existing customer databases.
The result? Increase in productivity of the sales team and improved decision-making process. But most importantly, positive feedback from the customers themselves.
Developing PoC with Low Code for a Tour Operator
To efficiently gather, centralize, and manage data is a challenge for any tour operator. Our client was not an exception. The company was seeking to get an internal software that will source information from third-party APIs and automate the travel itinerary creation process. Preferably, cost- and user-friendly tool.
The scope of work
Our experts ensured the client that all the requirements could be covered by Retool. And just in 40 hours a new software was launched. The tool had a flexible and easy-to-use interface with user authentication and an access management system panel – all the company needed. At the end, Retool was considered the main tool to replace the existing system.
Testing New Generation of Lead Management Tool with Retool
Our client, a venture fund, had challenges with managing lead generation and client acquisition. As the company grew, it aimed to attract more clients and scale faster, as well as automate the processes to save time, improve efficiency and minimize human error. The idea was to craft an internal lead generation tool that will cover all the needs. We’ve agreed that Retool will be a perfect tool for this.
The scope of work
The project initially began as a proof of concept, but soon enough, with each new feature delivered, the company experienced increased engagement and value.
We developed a web tool that integrates seamlessly with Phantombuster for data extraction and LinkedIn for social outreach. Now, the company has a platform that elevates the efficiency of their lead generation activities and provides deep insights into potential client bases.
Building an Advanced Admin Portal for Streamlined Operations
Confronted with the need for more sophisticated internal tools, an owner of IP Licensing marketplace turned to Retool to utilize its administrative functions. The primary goal was to construct an advanced admin portal that could support complex, multi-layered processes efficiently.
The scope of work
Our client needed help with updating filters and tables for its internal platform. In just 30 hours we've been able to update and create about 6 pages. Following features were introduced: add complex filtering and search, delete records, styling application with custom CSS.
Together, we have increased performance on most heavy pages and fixed circular dependency issues.
Creating MVP Dashboard for Google Cloud Users
Facing the challenge of unoptimized cloud resource management, a technology firm working with Google Cloud users was looking for a solution to make its operations more efficient. The main idea of the project was to create an MVP for e-commerce shops to test some client hypotheses. Traditional cloud management tools fell short.
The scope of work
Determined to break through limitations, our team of developers turned Retool. We decided to craft an MVP Dashboard specifically for Google Cloud users. This wasn't just about bringing data into view; but about reshaping how teams interact with their cloud environment.
We designed a dashboard that turned complex cloud data into a clear, strategic asset thanks to comprehensive analytics, tailored metrics, and an intuitive interface, that Retool provides. As the results, an increase in operational efficiency, significant improvement in cost management and resource optimization.
Elevating CRM with Custom HubSpot Sales Dashboard
Our other client, a SaaS startup, that offers collaborative tools for design and engineering teams, was on a quest to supercharge their sales efforts. Traditional CRM systems were limited and not customizable enough. The company sought a solution that could tailor HubSpot to their workflow and analytics needs.
The scope of work
Charged with the task of going beyond standard CRM functions, our team turned to Retool. We wanted to redefine how sales teams interact with their CRM.
By integrating advanced analytics, custom metrics, and a user-friendly interface, our developers provided a solution that transformed data into a strategic asset.
In 40 hours, three informative dashboards were developed, containing the most sensitive data related to sales activities. These dashboards enable our customer to analyze sales and lead generation performance from a different perspective and establish the appropriate KPIs.
Building a PDF Editor with Low-Code
Our client, a leading digital credential IT startup, needed a lot of internal processes to be optimized. But the experience with low-code tools wasn’t sufficient. That’s why the company decided to hire professionals. And our team of developers joined the project.
The scope of work
The client has a program that designs and prints custom badges for customers. The badges need to be “mail-merged” with a person’s info and turned into a PDF to print. But what is the best way to do it?
Our developers decided to use Retool as a core tool. Using custom components and JavaScript, we developed a program that reduced employees' time for designing, putting the data, verifying, and printing PDF badges in one application.
As a result, the new approach significantly reduces the time required by the internal team to organize all the necessary staff for the conference, including badge creation.